In February 2026, PayPal confirmed a significant security incident involving its PayPal Working Capital (PPWC) platform. Unlike a typical external hack, this breach stemmed from a six-month internal coding error that exposed sensitive data between July and December 2025.
Yes, but the impact was highly targeted. PayPal confirmed that while approximately 100 high-value business accounts had their data exposed, a "small number" of these users saw actual unauthorized transactions.
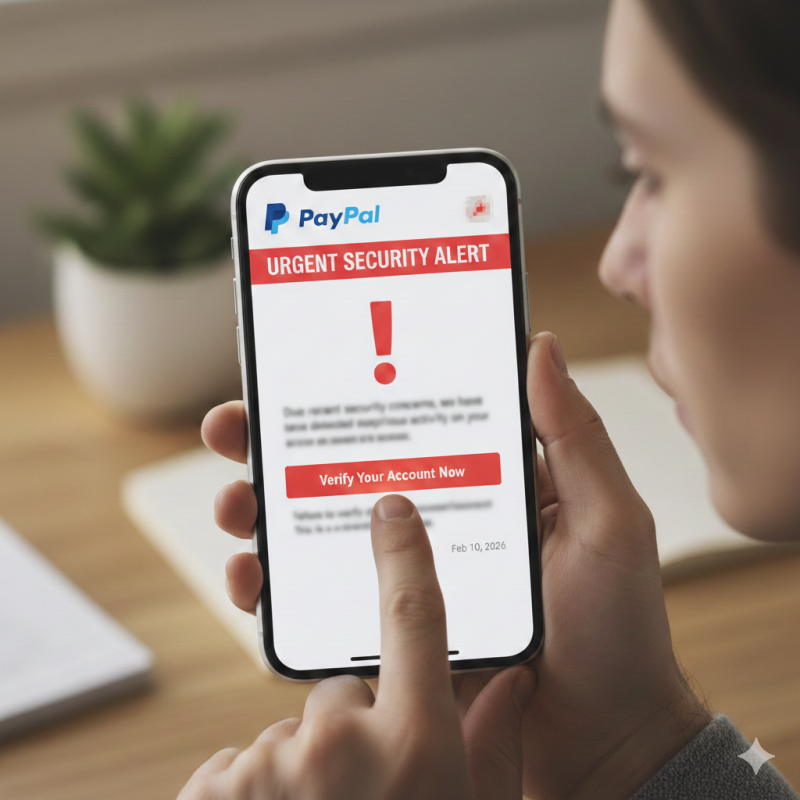
The good news? PayPal has already issued full refunds to those victims. If you haven't seen a strange charge or received a formal "Notice of Data Breach" letter (mailed around Feb 10, 2026), your funds are likely safe.
The leak involved "static" identifiers that are difficult to change, increasing the long-term risk of identity theft:
Despite the headlines, the answer is yes, with caveats. This wasn't a total system collapse; the core payment "vault" was not breached. The vulnerability was isolated to a specific loan application interface. PayPal remains a leader in "Zero-Liability" protection, meaning they—not you—shoulder the financial hit for security lapses on their end.
If you use PayPal, especially for business, take these four steps immediately to secure your account:
| User Type | Risk Level | Primary Action |
| Personal User | Minimal | Watch for phishing emails. |
| Business User | Moderate | Review 2025 transaction logs. |
| Loan Applicant | High | Freeze your credit and enroll in monitoring |
The Bottom Line: Be Careful With PayPal
The 2026 breach is a sobering reminder that "human error" in software updates can be as dangerous as any hacker. However, because PayPal has already covered the financial losses and isolated the bug, there is no need to close your account—provided you stay vigilant against the inevitable wave of phishing scams following this news.